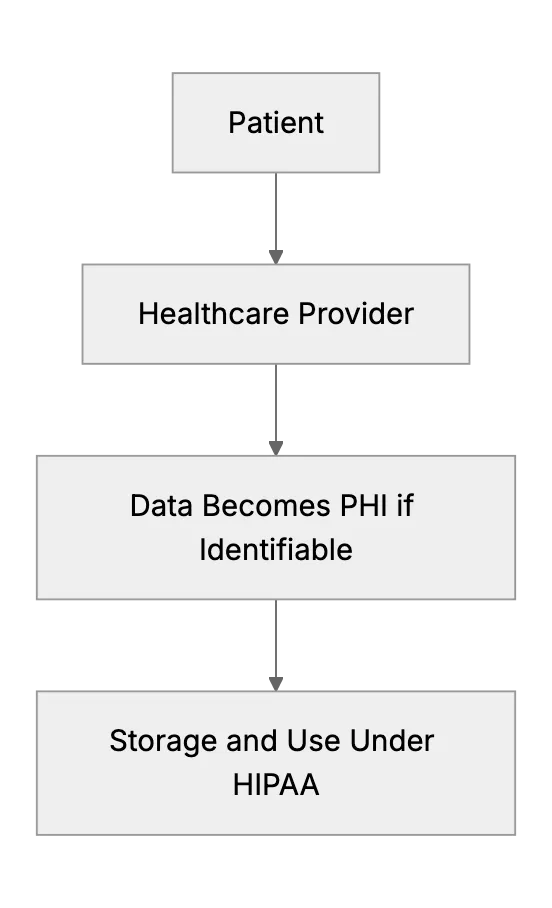
What Is PHI And How To Protect It
Learn what is PHI, how to identify it, and the needed rules for PHI protection
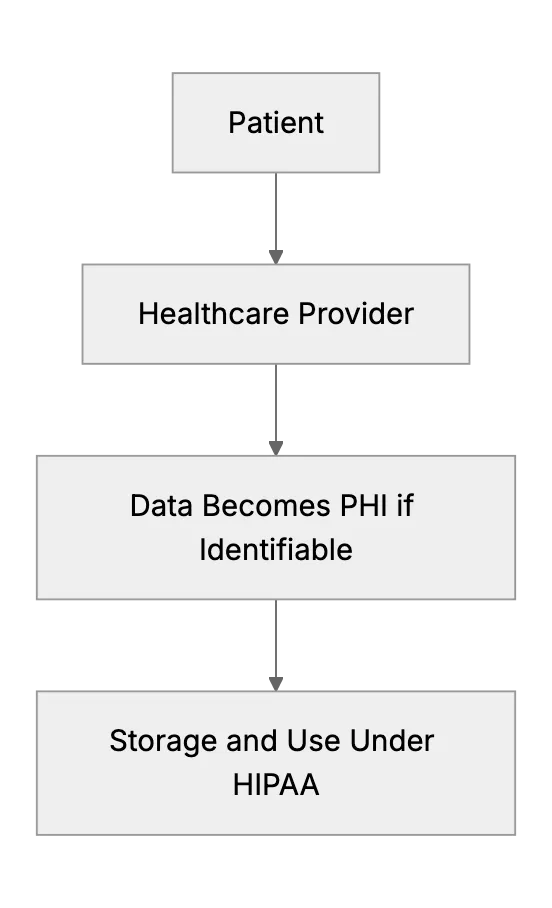
Learn what is PHI, how to identify it, and the needed rules for PHI protection
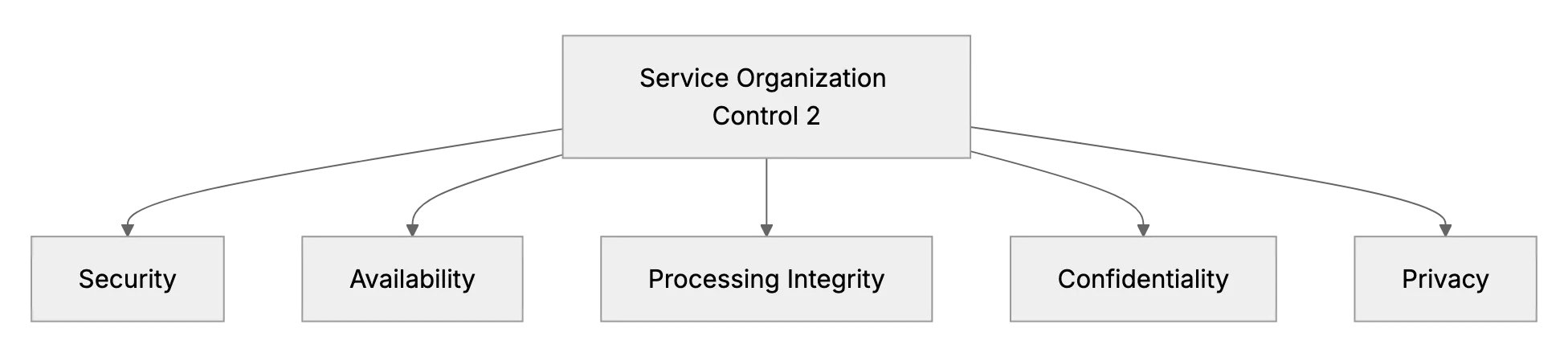
Learn about SOC 2, why it matters, who must comply, costs, and practical steps to keep customer data secure.
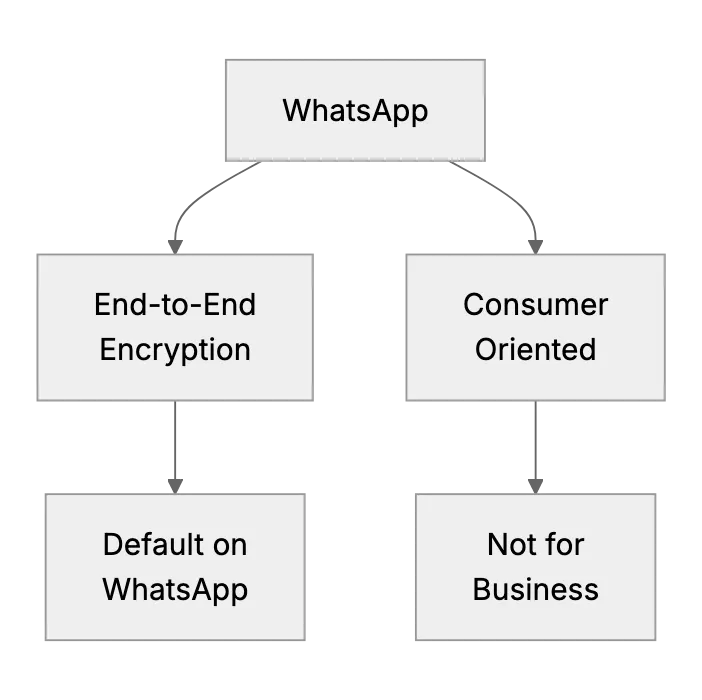
WhatsApp Messenger and Its Safety
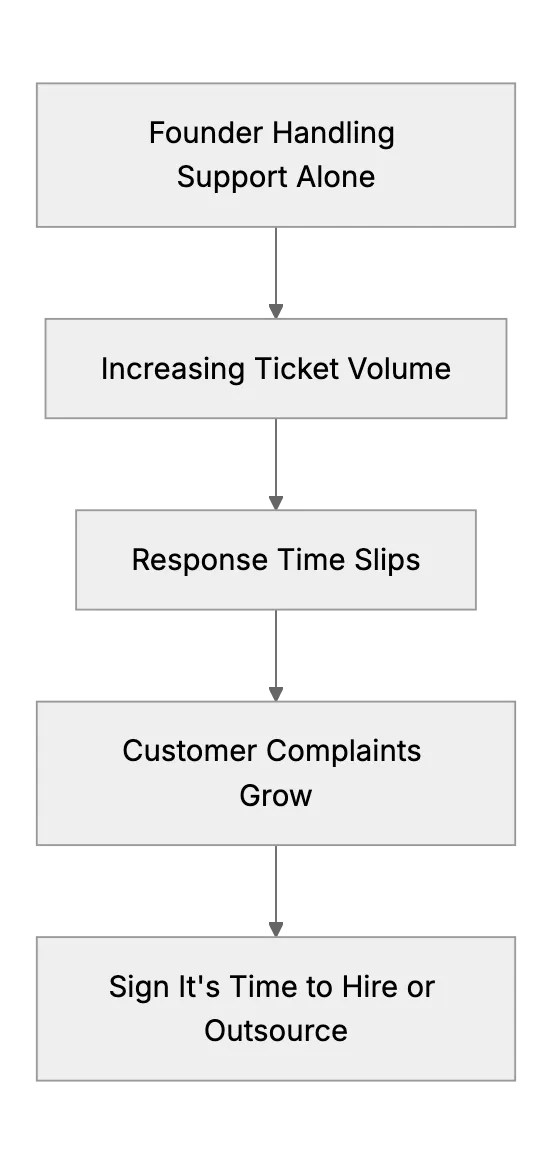
If you're a startup founder then you've probably wondered when it's time to hire a dedicated customer support rep. This article provides signs it's time to get help, along with creative solutions if you’re almost ready and tips on affording that first hire.
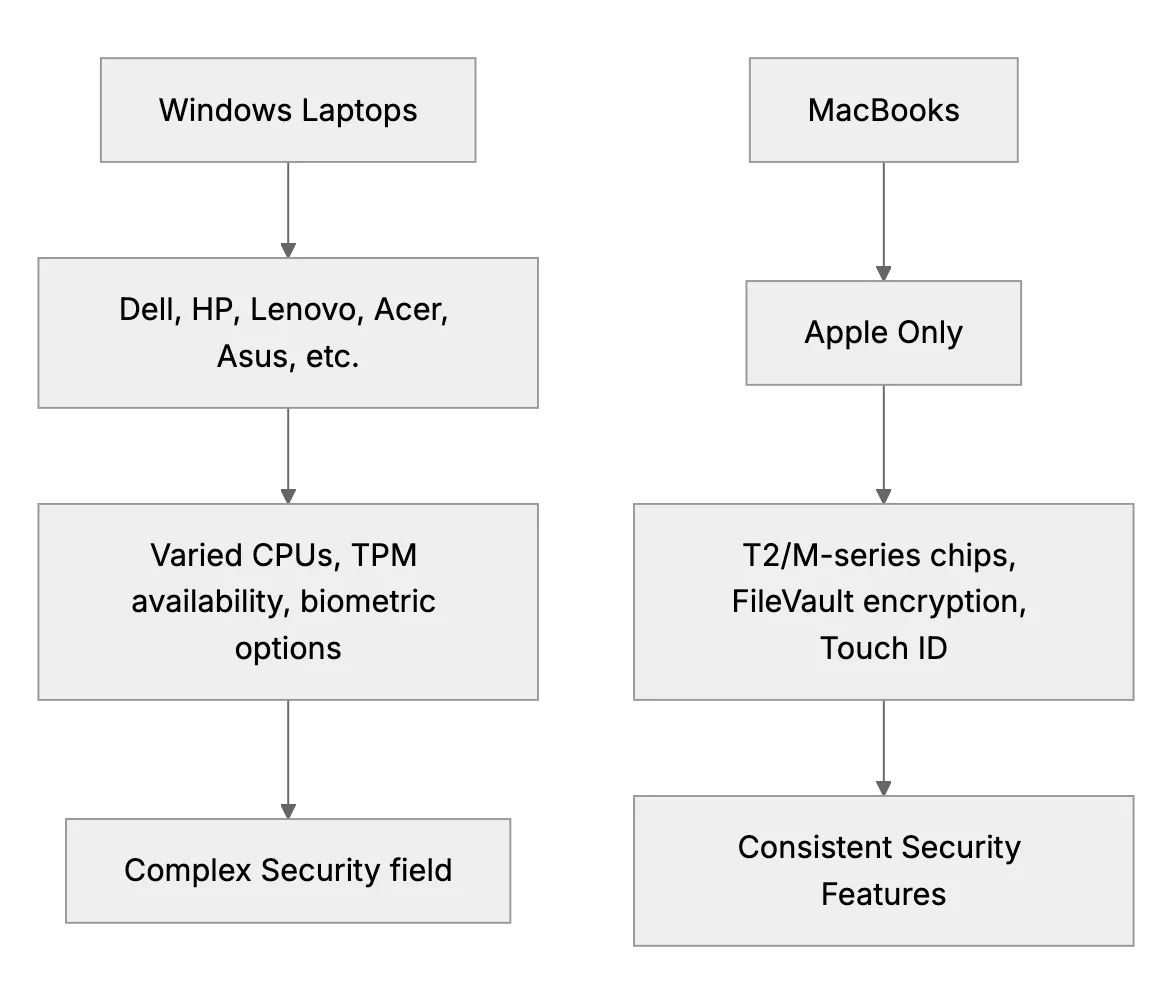
Find key differences between Windows laptops and MacBook security, and learn needed practices for keeping both secure.
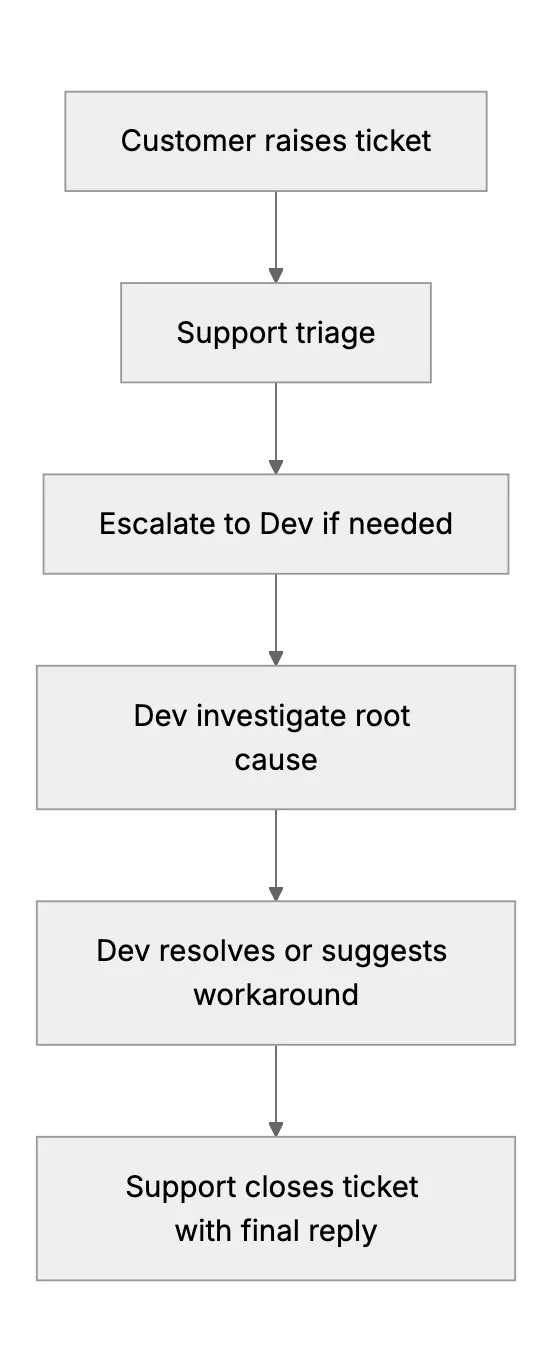
Tips on bridging the gap between support and engineering for effective collaboration and fast resolutions. Look at how to maintain good communication, set escalation paths, and track issues effectively.
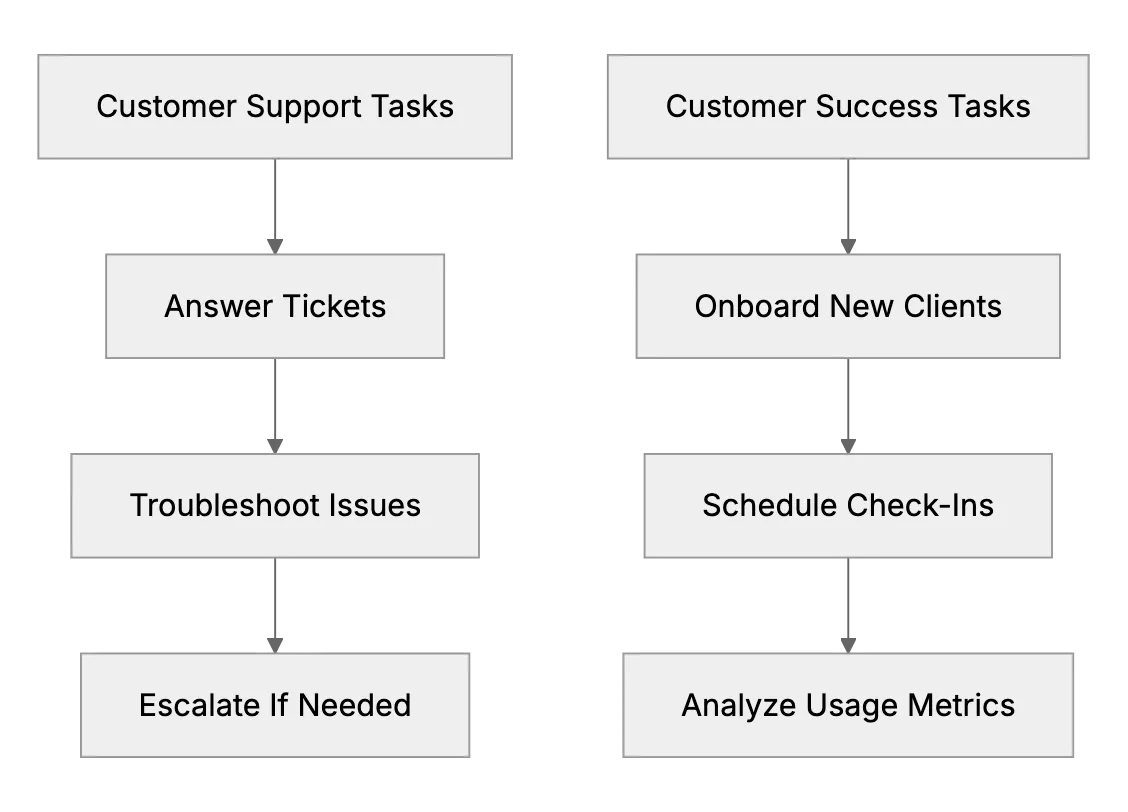
A thoughtful piece explaining the difference between reactive support and proactive customer success for small B2B startups. Helps founders decide when to focus on onboarding, training, and check-ins in addition to answering support tickets, showing direct revenue impact.
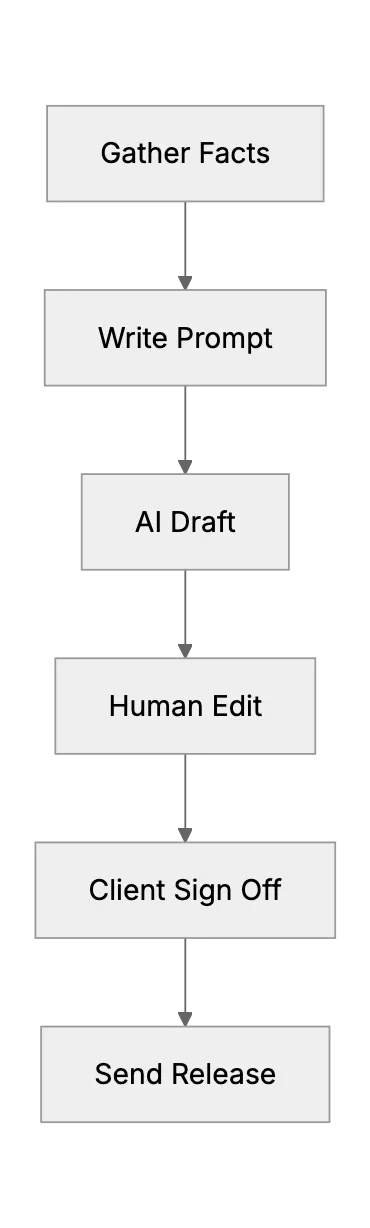
A step‑by‑step guide on using AI tools like ChatGPT to speed press release work for tiny PR teams.
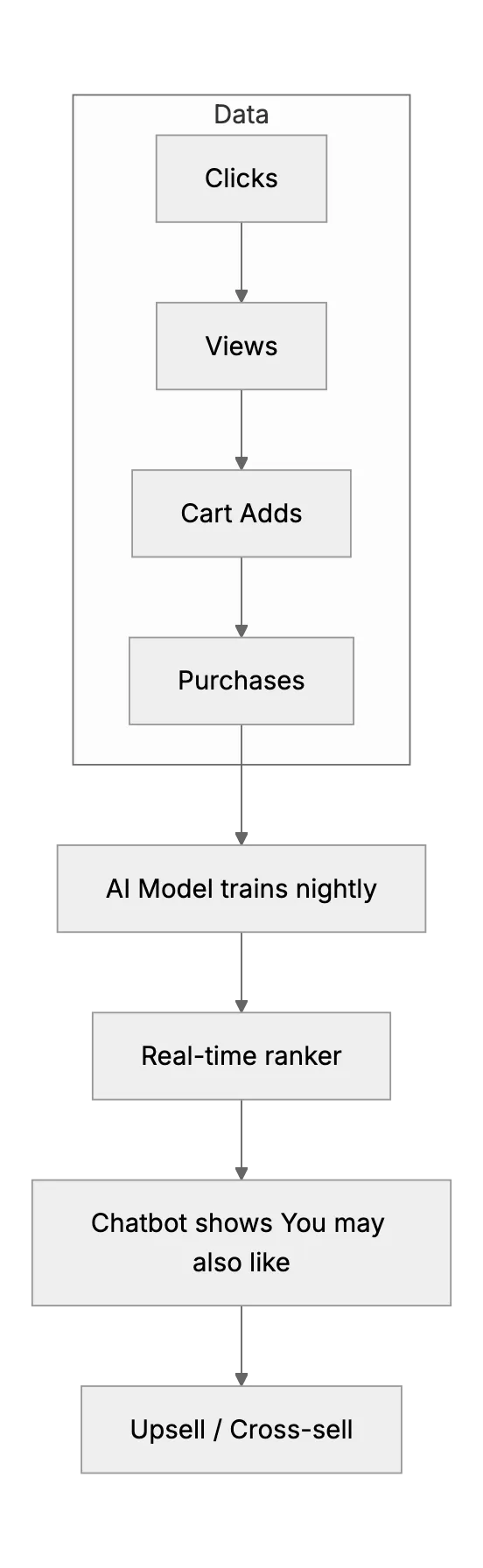
How small online retailers can use AI chatbots and recommendation engines to upsell, cross‑sell, and lift average order value.